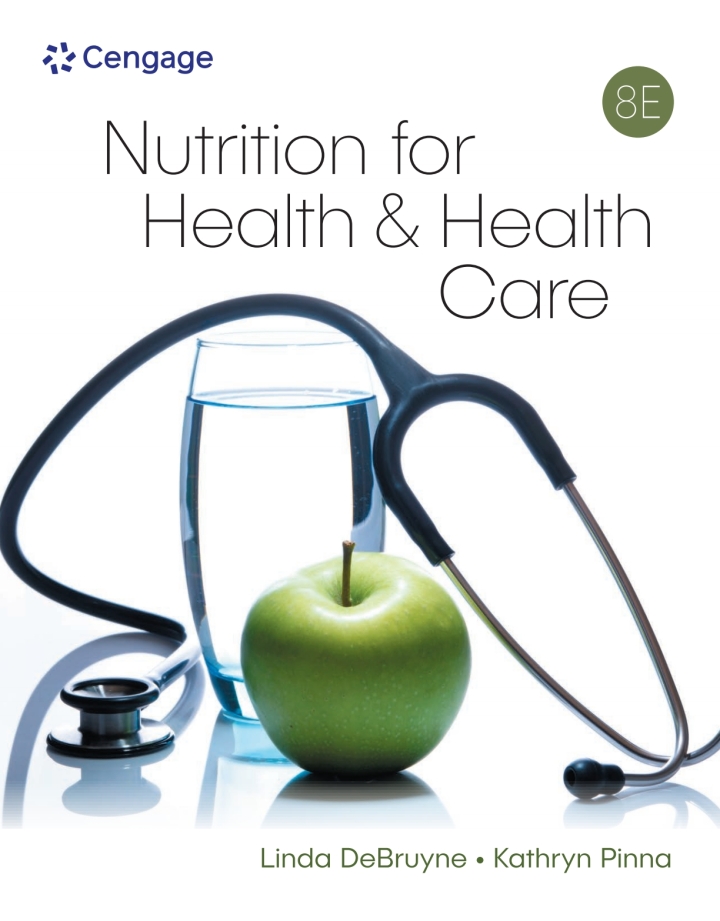
Featured Book
Nutrition for Health and Healthcare, 8th Edition - PDF
This updated 8TH EDITION demonstrates nutrition’s critical roles in maintaining health, preventing illness, and treating disease. Designed to engage and instruct both future nurses and health care professionals, the digital textbook is also helpful as an introduction for general nutrition students.
Psychology Books in PDF
Browse Our Complete Library
BROWSE COLLECTIONImmediate Access
Once you place an order, it is immediately emailed! You can also access your orders anytime from ‘My-Account‘
Tons of Books
We have thousands of downloadable textbooks, test banks, and solutions at huge discounts, especially for university students!
Thousands of Authors
Now you can search by the Author, ISBN numbers, or just the title of the textbook. More than 5000 textbooks avaialble!
Latest additions to our store

Engineering TextBooks

Medical TextBooks

Business eBooks
Latest Articles
Maximize Your College Experience: 10 Tips for Getting the Most Out of University
August 25, 2023You’ve no doubt heard terms like “the best four years of your life” when people talk about college. But enjoying your…
Author Stands Firm Against Request to Censor Racism References from Her Book
May 9, 2023The Scholastic case, which unfolded amidst the culture wars surrounding the surge in book banning within schools, sparked a resounding outcry…
Revolutionize Your Learning Experience with ChatPDF: The Ultimate Tool for Students
May 8, 2023How ChatPDF revolutionizes the student learning experience with AI tools, seamless PDF textbook integration, and collaborative features. Enhance your studies with…
Donations Accepted
September 5, 2019Donate Via Crypto Our main aim is to help all students save money, especially when college has become very expensive and…